Our Focus
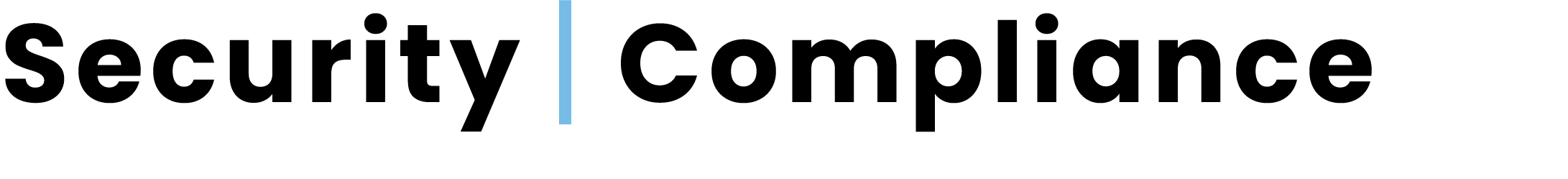
Organizational pressure to keep sensitive data and intellectual property secure are only increasing. Headline news associated with frequent and hard-hitting data breaches underscores the importance of staying on top of key security risks. And now with CEOs, CIOs, CFOs, CISOs, and security teams being held personally accountable – the stakes are higher than ever.
Guardian1℠
Network Penetration Test
It all starts with having a Penetration Test capable of quickly, comprehensively, and accurately assessing your Network for Exploitable Vulnerabilities
Risk Management
Which assets are at risk?
Once Network Assets have been scanned, data must be converted into actionable intelligence based on the Common Vulnerability Scoring
System commonly called CVSS
Testing
How do I assess where I'm exposed from an attacker's perspective?
There are two key areas to check: your “Network Attack Surface” and your “Personnel Attack Surface”.
PCI Compliance
Are we meeting requisite compliance standards?
Guardian1℠ is your first step in demonstrating that your network meets HITRUST and HIPAA compliance standards. Once vulnerabilities are identified through Penetration Testing, both HITRUST and HIPAA require that these issues be promptly remediated.
Guardian1℠ documents the process for addressing vulnerabilities based on their severity. Our reports and mitigation playbook give you the roadmap to fix Network vulnerabilities and keep ePHI safe.
To achieve HITRUST and HIPAA compliance, organizations must conduct regular, comprehensive penetration tests that cover both internal and external threats. These tests must be thorough, follow industry-standard methodologies, and result in actionable insights for improving security.
The findings must be documented, vulnerabilities must be remediated promptly, and the process must be repeated regularly and after significant changes to the environment.
Take action now with Guardian1℠as your first step to secure your Network and ensure your HITRUST and HIPAA compliance today.
To give our clients the most comprehensive vulnerability management solution on the market, we use The Industry’s Most Advanced Suite of Security Solutions. We deliver 360 degrees of protection that you can trust and count on for maximum Cyber Protection.
Our vulnerability management solution and complementary services overcome the frustration, lack of accurate results, and excessive costs associated with other mainstream security risk assessment tools
Threat Prevention
By using deep learning, we are able to predict and prevent Ransomware and any kind of threat – known and unknown – anywhere in zero time.
Join our Team
More consultants decide to join MSMNET SECURITY because we treat our consultants like family because they are FAMILY. Your contribution is appreciated and rewarded.